It’s just so fun to vibecode random apps from the comfort of the sofa but where should they live long term? As a committed Tailscale devotee I want someway to host them on my tailnet, available to my machines but not routable from the big bad internet (I’m not going to security review these things…).
Looking at options to connect containers, specifically rootless Podman containers, to the tailnet:
- Tailscaled Sidecar. This is the obvious implementation, each container gets an IP in the tailnet along with all the tailscale features like serve, funnel etc.
- Docktail is a cool app that automatically registers Docker containers as Tailscale Services. It joins the tailnet as a node and manages the advertisement of the services provided by containers on the machine, proxying conections through.
- TSDProxy is also Docker focused, but it creates a tailscale node per-container. That node runs a proxy through to the services offered by the container. I like the approach of node-per-container, but want something Podman focused.
I want each container to be its own Tailscale node, hosted on rootless Podman on Fedora Core OS, with container environments as clean (so ideally no sidecar) as possible, and with containers not routable from the network by default.
netavark-tailscale-plugin
Every container gets a tailscale identity with the only (except loopback) network device being a connection to the tailnet. 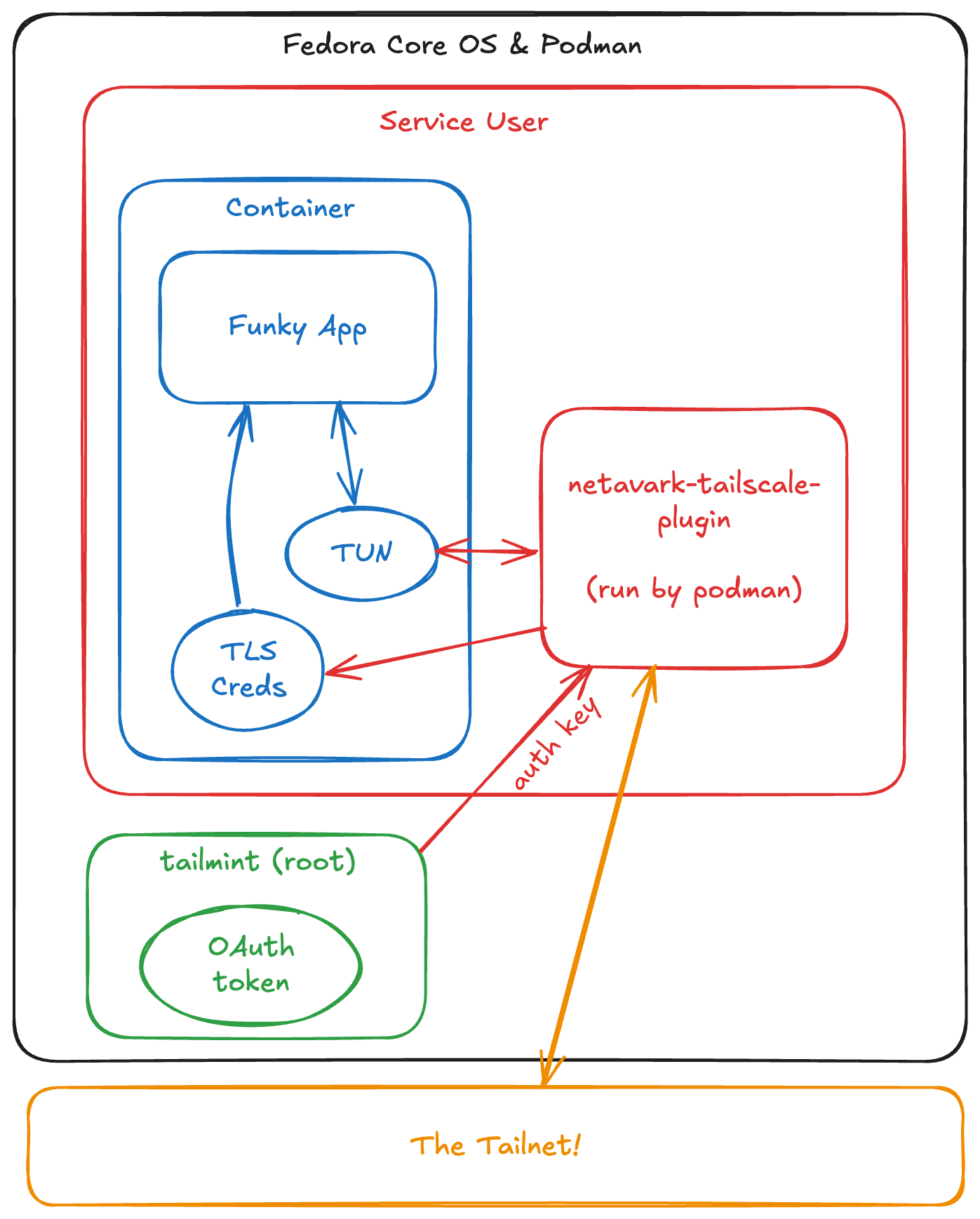
Rootless Podman containers commonly rely on Pasta configured by Netavark. Netavark supports plugins that can control how networking for a container is configured, and netavark-tailscale-plugin sets itself up to:
- Install a TUN in the container namespace as the only networking device available
- Join the tailnet as an ephemeral node, setting the container TUN to recieve all traffic
- Claim TS_HOSTNAME on the tailnet (and refuse to continue until that name is available to avoid being called service-1 after a restart)
- Containers don’t have a route to the host LAN at all - but you can configure a TS_EXIT_NODE and egress wherever your heart desires. This has been surprisingly useful to make the containers hosted in a Finnish Hetzner VM appear to the world as if they live in my Apple TV.
This works! With some nice little features like provisioning TLS certs it feels like a simple, neat way to get traffic in & out of my apps.
In my setup:
- tailmint provisions auth keys from an oauth token, keeping the oauth key away from the container users.
- quadsync gives me basic gitops, with some simple templating so I don’t have to have the tailscale config in every .container file
- netavark-tailscale-plugin makes all my apps appear as tagged devices on the tailnet, routable from all my devices.